Cybersecurity in Asia: How Can Businesses Protect their Interests?

Asia is 80 percent more likely to be targeted by hackers than the rest of the world.
Photo: Thomas Samson/AFP/Getty Images
Cyberattacks are growing in prominence: Ransomware attacks over the past two months infected networks of hospitals, banks, and utilities and transportation companies, among many others; and its effects were felt globally.
Mainstream news outlets and social media highlighted the attacks, speeding up the awareness and sense of urgency among businesses facing this evolving threat.
Asian Regulatory Landscape
In the Asia-Pacific (APAC) region, country-level cybersecurity commitments have been strengthening. Singapore claimed the top spot globally in terms of its commitment to combating cyber threats, according to the Global Cybersecurity Index 2017; other APAC countries such as Malaysia (3rd), Australia (7th), Japan (11th) and South Korea (13th) also scored well on the index.
While China launched a new nationwide legislation on June 1, 2017, and Singapore released a draft cybersecurity bill the following month, companies generally appear to be slow in adapting to the changing cyber landscape. The weaker cyber-risk mitigation efforts by businesses in Asia are significantly misaligned with the relatively higher cyber-threat level–Asia is 80 percent more likely to be targeted by hackers than the rest of the world.
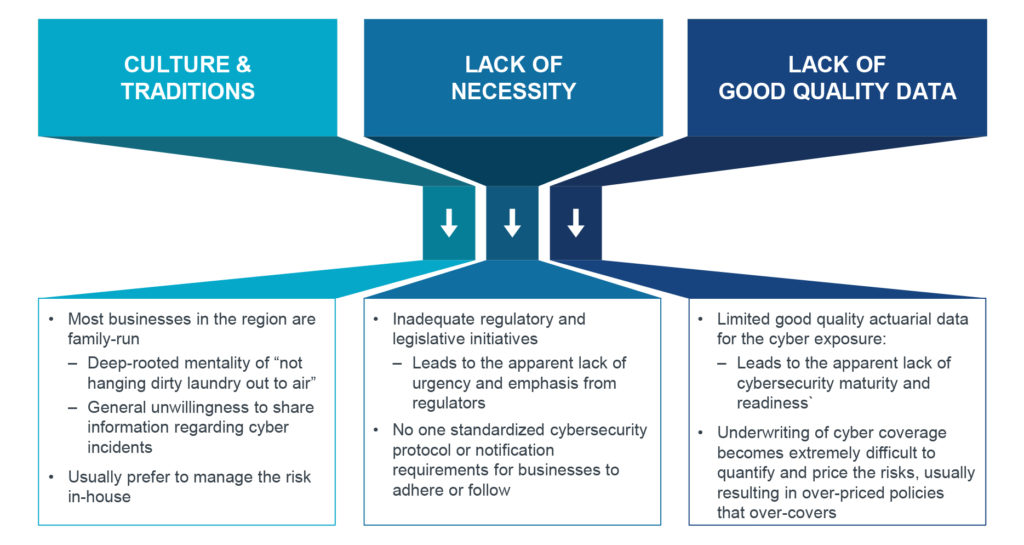
According to research published by the Asia Pacific Risk Center, the lower adoption of cyber insurance in Asia today is attributed to the general lack of awareness (Exhibit 1). The demand of cyber insurance in this region is heavily influenced by cultural factors and shaped by the inadequate regulatory and legislative landscape, leading to insufficient data and insights for purchases.
Exhibit 1: Key attributes to the low cyber insurance adoption rates in Asia-Pacific
The lack of information due to limited disclosure on the scale and frequency of cyberattacks in the region contributes to a false sense of cybersecurity that could cost businesses significant economic losses. This trend, however, may soon be reversed with the recent onslaught of high profile ransomware cyberattacks.
Asian Buyers’ Perspectives on Cyber Insurance
Misconceptions in the business industry have led to lower demand and adoption of cyber insurance, especially in Asia.
For example, based on experiences with clients and prospects, many organizations have responded that they do not have any cyber exposures, or simply that they are able to limit their exposures to cyber vulnerabilities such that cyber insurance would not be necessary. But they fail to recognize that any organization that uses computers or mobile devices connected to the network server has a potential exposure that cannot be neglected.
The continuously changing cyber landscape expands and extends exposures beyond data privacy and into network security systems, regardless of industries and the size of organizations. Should this be further ignored, disruptions to both network security and daily operations would cause severe financial impacts on businesses, especially the bottom line.
It has also often been argued that cyber insurance is too expensive and not within the organizations’ budgets, since there are already various policies in place. However, this perception can easily be addressed should organizations engage independent risk specialists to advise on a comprehensive yet fairly priced cyber-insurance coverage program bespoke to their needs.
Another cost angle to consider is the financial impact of business interruption in the event of a cyber incident—estimates of business interruption costs range between $1billion–$4 billion. Hence, transferring some of the risks to insurance and capital markets may eventually yield greater cost savings in the long run.
Enhancing Cyber Resilience is an Enterprise-Wide Responsibility
Cyber risk should be recognized as an enterprise-wide risk and cyber insurance—a risk mitigation tool—should supplement risk management measures, such as endpoint security defense and business continuity plans, so as to build and enhance cyber resilience within the organization (Exhibit 2).
Exhibit 2: A balancing act of key components to enhance cyber resilience
Effective endpoint security management. Endpoint security responses are usually the first line of defense against cyberattacks. They follow a definite level of compliance standards to protect computer networks and individual devices, which are commonly exploited as access points into corporate networks. In view of the evolving nature of cyber threats, updates and upgrades must be made to traditional endpoint security. In recent times, more advanced intelligence, such as that from the dark web, has been collected to research and analyze trends and technical developments, therefore ensuring “smarter” and quicker detection, investigation, remediation, and recovery.
Leverage risk transfers. As illustrated earlier, cyber insurance is one key component to enhance cyber resilience, as it transfers some of the risks to the insurance and capital markets and offsets some of the costs. The necessary step to implement this component is to first educate and nurture businesses, so as to engage in deeper, more meaningful and more conclusive conversations about cyber risk. Businesses need to be well aware of the potential impacts cyber threats may bring about, as well as the reassurances from suitable policies, before they can accept and adopt cyber insurance coverage as a necessary risk-mitigation strategy for their organizations.
Make business continuity management plans. Finally, business continuity management (BCM) is an all-inclusive process that enables organizations to better prepare in advance for, and respond to, potential crisis situations that may lead to business interruptions. The main objective of BCM in this context is to put in place business continuity plans (BCPs) to ensure the continuation of critical functions in the event of a cyberattack. Therefore, it is a business imperative to identify and determine the criticality of each business function, information and communications technology (ICT) applications, and databases and services to ensure resources are used effectively for prompt recovery executions of key functions. This is then followed by conducting fire drill exercises to familiarize the organizations of the processes involved to effectively execute the BCPs should the need arise. As part of the ongoing process of BCM, these BCPs will require regular stress-testing and updating so as to improve efficiency and effectiveness.
Evolving with the Risks and Uncertainties Ahead
We believe that cyber resilience can be enhanced via this three-pronged approach, thereby reducing significant costs and recovery downtime to business interruption.
Business leaders should not be lulled into being overly confident—they must take active steps to prevent and mitigate cyberattacks by applying the right resources and developing strategic contingency plans to effectively respond when an attack occurs.
Organizations also need to strike the right balance between cybersecurity investments in endpoint security management and BCP, as well as securing the appropriate cyber insurance coverage suitable to the relevant and unique needs of their industry and organization.
It is critical for businesses to continuously assess and improve the understanding of their cyber-risk posture so as to make strategic decisions around business operations, develop cyber resilience, and better prepare the organization for uncertainties in our increasingly digitized world.