Bug Bounty Programs: Will Asian Companies Take the Leap?
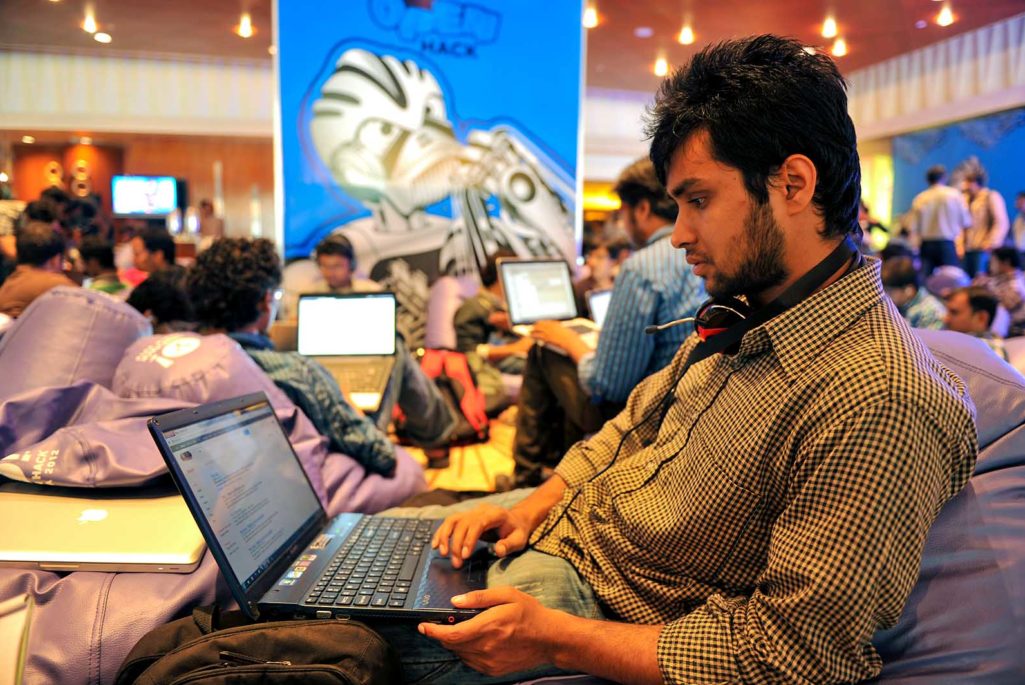
A participant uses his laptop computer during the fifth edition of Open Hack India, a 24-hour non-stop hacking event organized by Yahoo! India R&D, in Bangalore on August 11, 2012. Over 700 Indian software developers from across 20 states participated in the marathon Open Hack event.
Photo: Manjunath Kiran/AFP/GettyImages
Bug bounty programs are crowdsourcing initiatives developed by organizations that invite the public to aggressively hunt for and report on flaws in their system or software in return for a reward. These bounty programs are meant to augment the organization’s security teams with early notifications of hidden bugs and flaws in company software, hardware or services before they are released to the general public.
Bug bounty can be profitable for a skilled security researcher; and indeed a significant proportion of bug bounty hunters hail from Asia, owing to the strong engineering focus in many Asian economies, particularly India, Pakistan, the Philippines and Malaysia.
Apple recently launched a controlled bug bounty program, offering a maximum of $200,000 per vulnerability found. Meanwhile, a renowned bug bounty brokerage firm, Zerodium offered $1.5 million per vulnerability found. Companies across different industries are increasingly engaging in bug bounty programs, including banking and financial services, telecommunications, health care, consumer, marketing, automotive and entertainment, among others. In Asia, companies such as Indian mobile wallet Paytm and cab aggregator Ola have launched bug bounty programs.
However, despite the presence of a thriving Asian bug bounty hunter community, many companies don’t have the capacity and resources needed to implement such a program. Many companies are too conservative in nature and find the idea of asking strangers to penetrate their business and reveal its weakness to be unthinkable. This stems, in part, from Asian culture, where weakness isn’t exposed in public.
Finally, in Asia, companies often do not see the return of investment on bug bounties due to the complexities of setting up such a program, which can involve legal, cyber, communication, benefits and a rewards team.
Benefits of Bug Bounty Programs
Companies should consider bug bounty programs for a number of reasons.
Vulnerability management (finding bugs). Bug bounty programs are meant to discover and fix vulnerabilities before they become public and cause financial and reputational damage. Moreover, it’s better for these vulnerabilities to be discovered by a bug hunter rather than a “black hat” (a hacker with destructive intentions).
Labor and skills. As this is a crowdsourcing initiative, companies can have a large number of people from different parts of the world working for them. They will see various skill sets starting from “script kiddies” (using others’ code instead of developing new code) to the world’s renowned security researchers and “white hats” (ethical hackers who hack with authorization).
Save money by paying only for results. Hiring an expensive professional firm to conduct vulnerability and penetration results in charges, regardless of whether it finds a bug. The pay-for-results method is paying for the successful discovery and reporting of a well-defined exploitable vulnerability.
Compliance. Various standards and regulations (for example, PCI DSS requirements on web security assessment) mandate regular and independent penetration testing to be conducted. Bug bounty vulnerability reports would satisfy many of them, particularly since such standards typically do not define a specific methodology for the penetration testing required.
Businesses in Asia will be more secure if they adopt bug bounty programs to uncover vulnerabilities.
Encouraging good behavior and public relations. Bug bounty programs encourage hackers to report vulnerabilities before they publish them to the public. Many other hackers publish all their findings online for recognition and credibility among their peers, or they sell the vulnerability (or its exploits) to cybercriminals on the black market. Bug bounty programs ensure hackers get rewarded only when they follow responsible disclosure agreements, and they enhance an organization’s relationship with the public, researchers and hacking communities. This is as opposed to the situation ransomware developers create, where companies have to pay ransom to unlock their data (which is basically an act of rewarding bad behavior).
A Few Challenges
While bug bounty programs have their benefits, there are various challenges involved in implementing them.
Overhead “running cost.” Running a bug bounty program can be costly if not properly managed. The programs require deep technical, communication and financial skills, and attracting the best security researchers requires premium awards. If an organization does not have the required resources to run a bug bounty program in-house, then it is recommended they engage a bug bounty brokerage or bug bounty SaaS (software as a service).
Lack of enforcement. Many bug hunters may not follow the organization’s rules of engagement and instead try unauthorized methods (e.g., social engineering) to find vulnerabilities. Since they operate in an uncontrolled environment, some bounty hunters could exploit vulnerabilities and perform lateral movements to find others. Vulnerabilities could worsen if they run Distributed Denial of Service (DDoS) attacks that can make online services unavailable. Most commonly, these attacks occur when a network is flooded with information, resulting in the server becoming overloaded, unable to process requests, and becoming inaccessible for users, for example.
This issue can be avoided if bug bounty programs properly define the rules of engagement. Using a controlled bounty environment, where researchers are thoroughly vetted and hold a higher reputational rating, is also recommended (for example, Bugcrowd).
It can backfire. When researchers notify an organization with a high severity vulnerability and do not get a proper response, they normally cause more damage by publishing the vulnerability online. For example, this could happen in instances when a vulnerability report is sent, but there is no response from the organization; if an award has been refused or its value reduced; if an out-of-scope vulnerability is not rewarded; or when the researcher does not receive public acknowledgement from the organization.
A few organizations get around this challenge by offering closed bug bounty programs that require an invitation. Apple, for example, has limited bug bounty participation to a few dozen vetted researchers.
Double dipping. Even if researchers who have reported an exploitable vulnerability have been paid the bounty, there is no guarantee that they will not resell the same vulnerability on the black market after receiving their award.
This issue can be checked by implementing immediate payment instead of only after fixing the vulnerability. Organizations can also consider using a private crowd that only leverages high-quality researchers with good reputations.
Black hats are also invited. While bug bounty attracts many talented researchers and white hats, it also attracts black hats who are there to take advantage of the crowd in order to go undetected. For example, a black hat hacker knows that a massive number of probes and scans are happening during the bounty time frame and the organization’s SIEM (security information and event management) is overwhelmed with millions of events, allowing his or her actions to blend with other legitimate scans.
Securing the Future
Organizations in Asia will become more resilient, secure and safe if they start adopting bug bounty programs and acknowledging their vulnerabilities before others do. The Asian region is home to talented security researchers who are out there waiting for the opportunity to showcase their skills, while at the same time getting rewarded for it.
However, building a reliable bug bounty program can be overwhelming and financially onerous for many organizations, and therefore, companies should consider bringing on board external vulnerability coordination and bug bounty platforms that link businesses with security researchers. This will ensure that a smooth and reliable program is being implemented by experts, and at the same time, it will help limit companies’ costs and keep budgets in a manageable range.
Bug bounty programs are useful if developed correctly with the right management support, resources and governance. They work best if bound by time and if delivered by professional service providers. A good program can prevent an organization from being in the headlines for the wrong reasons.
The views and opinions expressed in this article are those of the authors and do not necessarily represent their employer’s positions, strategies or opinions.




