Planning for Cyber Resilience

Cyber risk is a cumulative problem; significant new cyberattacks continue to emerge while older attack methods persist.
Photo: Leon Neal/Getty Images
It’s just about a cliché these days to say that it’s not if your organization will be affected by a cyber event, but when. Or worse yet, not when it will be affected, but when you’ll discover it.
And yet, despite the increased attention on cyber risk over the past decade, most organizations are still not building strategies that bring resilience in the face of this evolving risk. Those that do aim for cyber resiliency can help their companies withstand the inevitable cyberattack and effectively manage its consequences.
Consider business interruption. Losses can quickly mount after something as common as malware sent through a simple email attachment affects your or your supplier’s systems. Still, it is difficult for companies to get their arms around cyber-related business interruption losses. Less than one-third of companies have confidence that their organizations are prepared to handle a business interruption loss from a cyber event, according to a poll taken during a recent Marsh webcast.
Difficulties Managing Cyber Business Interruption
Cyber risk is a cumulative problem; significant new cyberattacks continue to emerge while older attack methods persist. The global WannaCry ransomware attacks and the global NotPetya destructive-ware attacks from earlier this year underscored the significant challenges facing organizations. These attacks caused significant business disruption, with potential insured losses expected to exceed $100 million and uninsured losses tallying well beyond that.
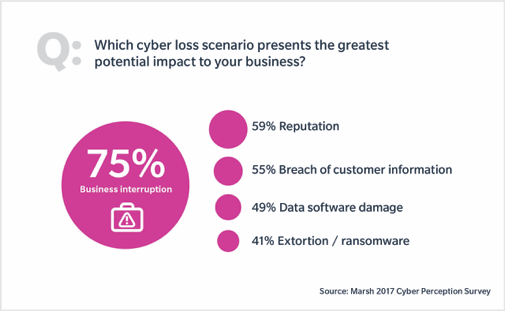
For good reason then, business interruption is seen by many as the most worrisome cyber loss scenario: More organizations view business interruption as a top cyber risk than any of a dozen other choices—including breach of customer information and reputational damage—according to a recent Marsh survey (the full results of which will be released later this year).
But if it is so worrisome, companies need to do a better job planning for it. Cyber business interruption losses are difficult to predict ahead of an event because costs depend on such factors as the specifics of the event, the organization’s business model, its response, and more. A plan that includes financial quantification, effective mitigation measures, and appropriate risk finance options should be part of a coordinated effort to build cyber resiliency.
There are two factors at play as to why domestic and global organizations will face increasing difficulties with cyber business interruption risks. First, organizations’ networks and network security programs are becoming more complex—and complexity typically increases vulnerability. Businesses are stitching together more systems of varying ages and with different levels of vendor lifecycle support. At the same time, much sensitive data is strewn across millions of employee-owned devices. This makes the systems and the data difficult to manage.
The second challenge is with Internet of Things devices, 20 billion of which are expected to be connected to the Internet in the near future. Last year’s Mirai botnet—malware designed to target and control online consumer devices such as IP cameras and home routers—marked a turning point for IoT risk. The attack raised questions such as: Who holds the liability when something goes wrong with IoT devices? How do we account for related business interruption losses? Is enough being done to secure the devices?
Building Toward Resiliency
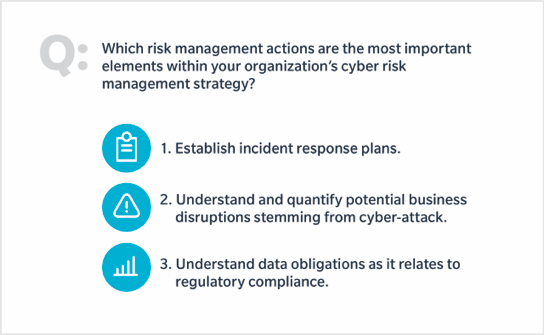
On the positive side, organizations’ cyber risk management strategies seem to be leaning in a direction that will benefit business interruption planning. It was heartening that respondents to a Marsh webcast poll raised incident planning, quantification of losses, and regulatory compliance as keys to their organizations cyber risk management strategy.
Organizations can build on such steps to bolster cyber resiliency efforts. Remember:
Resilience does not mean that cyber risk has to be eliminated—it won’t be. Instead, resilience refers to a company’s ability to both withstand a cyberattack and effectively manage the consequences. A critical step is to make sure that cyber risk is properly addressed at the corporate level, beyond IT and security.
Much more can be done to help senior leaders understand that cyber risks are not technical problems that firewalls and patches (though important) can solve alone. They need to be shown that these are strategic risks that must be managed by understanding the business impact and taking the multiple steps needed to ensure resilience before, during, and after an attack.