The Top 5 Cybersecurity Mistakes Companies Make and How to Avoid Them
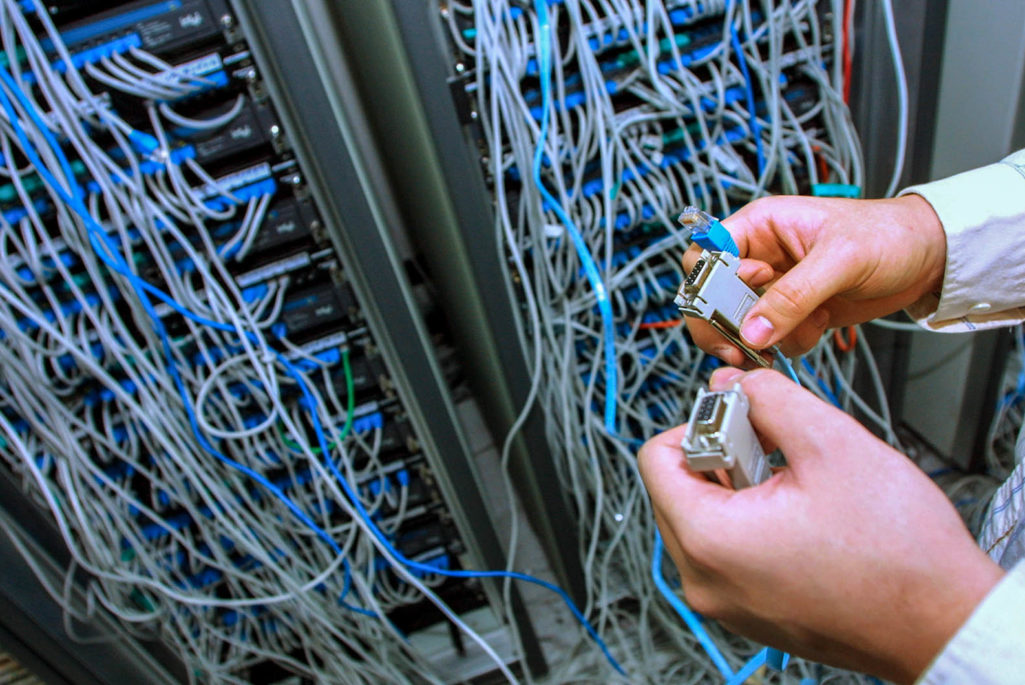
An engineer at South Korean anti-virus firm AHNLAB.com checks the company's systems after the 'SQL Slammer' computer worm attacked Internet servers in January of 2003. At the time, the quickly multiplying worm nearly cut off South Korea's internet access.
Photo: Chung Sung-Jun/Getty Images
Cybersecurity requires a holistic organizational approach. From the leadership to each rank-and-file employee, a concerted effort must be maintained to establish, execute and follow-through with a plan to address cyber-risk management from all corners of the organization.
Although there is no one-size-fits-all plan for organizations’ cyber-risk management needs, there are basic, core principles every organization should adhere to in order to maintain a solid security posture in the face of persistent attacks.
Below are the five most common mistakes organizations make when it comes to defending their assets from cyber adversaries and how to prevent them.
Mistake #1: Assuming you’re not a target. From Wall Street to Main Street, whether large or small, companies in virtually every industry are vulnerable to attacks. Often, however, the stories that make the news headlines are about theft of credit card data or personally identifiable information. As a result, companies that don’t handle this type of data often believe they are not a desirable target for cyber adversaries. In reality, adversaries are conducting massive campaigns in every sector of the economy to penetrate networks and exfiltrate information and assets. Organizations certainly have information of value; they are in business, and customers are buying what they have. Every organization needs to recognize that fact and work to detect and prevent the potentially devastating damage cyber attacks can cause.
What if the company network was damaged beyond repair for a couple of weeks? What if, as a result, payroll couldn’t be paid, communication with clients was stalled or product websites shut down? What if a hacker could sabotage a company’s most vital equipment? Increasingly, adversaries are not only taking data, but using digital attacks to physically destroy real assets.
Solution: Take this risk seriously. Once your company’s leadership starts addressing cybersecurity as a business priority, find qualified security experts to conduct assessments and testing that identifies vulnerabilities throughout the company’s technology, people and processes.
Mistake #2: Approaching security as just an IT issue. This is not “the CIO’s problem.” Technology is a part of the solution, but the holistic response requires comprehensive strategy, policy and process. While the CIO or CISO may ultimately be the “accountable executive,” everyone in the organization, especially the C-suite, owns the data and has a responsibility to protect the company’s core assets.
Companies need to focus not only on protecting personally identifiable information (PII) but also on guarding intellectual property, trade secrets, research and development and more. Cybersecurity attacks impact organizations’ bottom line, financial position, reputation and operations, and having clear policies and processes in place will help companies and their employees to most effectively respond.
Solution: The risk to the company via the cyber vector should be elevated to the highest levels of the company’s decision-making body, including members of the board on a periodic basis. While business leaders aren’t required to know technical details, they must have enough threat awareness to be able to help formulate adequate cyber-response plans and allocate sufficient resources to carry out these plans. Through training, education and simulations, teach the whole company—from the top down—how to identify threats and prevent and recover from attacks.
Cybersecurity doesn’t happen in a vacuum. Just as the threats are interconnected, so are the solutions.
Mistake #3: Neglecting to understand and update your network. Companies will never be able to prevent every attack; networks and the target space are too vast and there are too many opportunities to get in. But failing to understand the architecture of your network and keep your software updated opens the door for an adversary to breach the system with little-to-no resistance.
Solution: At the enterprise level, the IT team must implement strong protocols to ensure all software is updated in a timely manner. The organization must know where its critical data is, how big the network is, where the egress points are and how the network is segmented. A lack of understanding of the basic network principles and standard “network hygiene” puts the company at unnecessary risk. Have a sense of urgency and get it done.
Mistake #4: Relying solely on anti-virus technologies. In today’s sophisticated threat landscape, anti-virus technologies alone are not sufficient to prevent persistent and advanced attacks. Adversaries evolve their tradecraft faster than security companies can update their tools. What is compounding the challenge is that attackers increasingly employ malware-free intrusion tactics. In fact, less than 40 percent of attacks today involve malware. You cannot rely on security at the perimeter alone to keep the enterprise safe.
Solution: Anti-virus software is still useful and must be kept up-to-date. However, responding only to threats that have already been identified is like being a bank guard who lets a robber come in because the police haven’t released a description of a robbery suspect yet. A good bank guard knows to look for malicious activity anywhere it might be found. Traditional anti-virus solutions may catch run-of-the-mill malware, but are no match for advanced adversaries going in with stealthy intrusion tactics. Organizations need to employ solutions that identify adversary objectives and the effects of the attack, even if there are no known signatures.
Mistake #5: Failing to monitor your enterprise endpoints. The conventional “defense-in-depth” model has focused on defending the perimeter of an organization. Today, more often than not, adversaries are finding ways to penetrate the network and execute code at the system’s endpoints. We are also witnessing a continuous and ever-evolving sophistication in adversary tradecraft beyond anything we’ve seen before. Watching the perimeter only allows for “silent failure.” That is, once an adversary is inside, he operates freely without threat of detection because nobody is looking. He will operate with impunity, posing grave danger to your organization.
Solution: Employ technologies that monitor endpoints continuously. Endpoint visibility is critical for making the transition from reactive security to proactive hunting and detection. Aggregating large swaths of data and looking for anomalous behavior across the enterprise will help to identify indicators of attack. If you can identify adversary activity expeditiously, you can isolate and mitigate the attackers impact on your network.
Cybersecurity doesn’t happen in a vacuum. Just as the threats are interconnected, so are the solutions. A cohesive top-to-bottom plan is what gives companies the best chance at raising the bar on security and keeping the bad guys at bay. Cyber-defense tactics and tools cannot remain static. They must be tested, improved and evaluated on a regular basis. The threat never sleeps, and companies can’t afford to be asleep while the adversary threatens their existence.




