‘Cyber Pearl Harbor’ Isn’t Coming. The Real Threat May Be More Mundane.
An interview with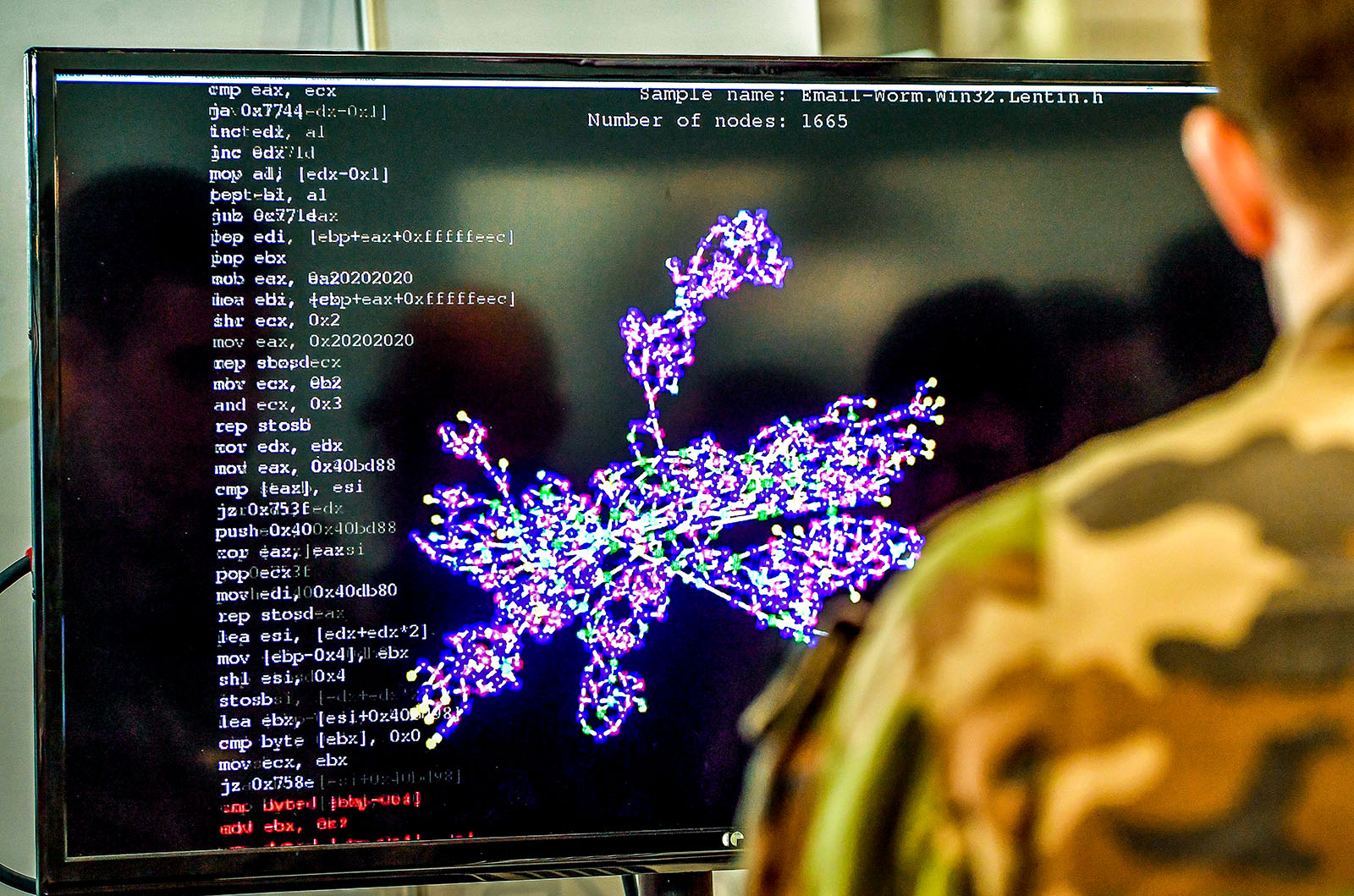
A member of the military specialized in cyber defense works on a computer in Lille, France. What are the challenges facing those who study and work in the field of cybersecurity?
Photo: Philippe Huguen/AFP/Getty Images
News reports about impending cyber threats are a fixture of technology coverage these days. One might assume that cyber warfare is always happening, out of sight but constantly chipping away at the foundation of the international order. But does the data support this view?
In a 2018 paper titled “How We Stopped Worrying about Cyber Doom and Started Collecting Data,” Brandon Valeriano, the Donald Bren Chair of Armed Politics at the Marine Corps University and Cybersecurity Senior Fellow at the Atlantic Council, along with a co-author, contested this view of the cyber threat landscape. BRINK News spoke with Dr. Valeriano about the challenges facing those who study cybersecurity and the risk of overhyping unrealistic cyber threats.
BRINK News: One of the key issues that you identify is that we’re awash in inaccurate representations of the cyber threat landscape. Why is this a problem?
Brandon Valeriano: The main issue is that if you’re prepared for the worst case, you can omit the more basic, mundane issues. There’s a lot of conflict going on in cyberspace, but the majority of it is espionage and other low-level, disruptive operations.
BRINK: One idea you single out in your writing is the false perception that data on cyberattacks are “uncollectable and mainly classified.” Your counter argument is that, in fact, there is a lot we can learn about malicious cyber behavior and the actors behind it. Could you explain why that’s the case?
Dr. Valeriano: It’s fairly easy to place blame. You get to understand who the adversary is, what they’re doing, the times they operate and the things they like. It’s fairly easy to know who’s doing what. The challenge is legal attribution. It’s very unclear who is ordering these operations. Is it Russian President Vladimir Putin? Is it North Korean Chairman Kim Jong Un? That’s the bigger challenge. We can know who’s doing what, but it doesn’t exactly mean that we know exactly where to place the blame in terms of legal authority.
The other thing is that cyber — in terms of how it operates — is a very public act. Bad actors go into a network and try to take it down, try to harm it, try to harass it. By doing that, they make the operation overt. So while cyber operations are covert — meaning they are undeclared — they are simultaneously out in the open, and we can learn a lot about them.
There is no such thing as perfect data. But as an academic, as a researcher, I want to be able to say, “I know because of this, this, and this.” I may be wrong, but I’m making an inference based on evidence and data. And that’s how we operate as social scientists. We do the best we can based on the data we have.
BRINK: One of the things you write is that language and conceptual frameworks on cybersecurity can become self-fulfilling prophecies. What do you mean by that?
Dr. Valeriano: If you believe that the threat is out there and that it’s going to harm us, you’re going to find every opportunity you can to paint any example as something that proves you right. And that’s not how social science should operate. Of course, there is bad data, and there are bad researchers. But an honest social scientist will go any way the data leads them. That’s what we’re hoping for more of.
When I started collecting data on cybersecurity, I thought it would be the future of warfare and a new way that rivals deal with each other. What I’ve evolved toward, by studying a lot of data over the years, is that this is a form of political warfare, done at the level of espionage or covert operation, that is more akin to sanctions than to decisive battles. The idea of cyber operations being decisive and changing the behavior of the adversary is an unknown. We haven’t understood how countries and individuals react to cybersecurity threats.
BRINK: You have written that cyber capabilities are more likely to be a mundane piece of a state’s arsenal than a game-changing new element. But in your last answer, you mention that we don’t know how actors respond to cyberattacks. Isn’t there room in this gap in understanding for something to emerge that will constitute significant change?
Dr. Valeriano: By doing behavioral analysis, experiments and surveys and by working with the military and talking with people who are making key decisions, we can learn how cyber capabilities fit into a framework of operations. War games, in particular, are really interesting for learning how people will behave when confronted with cyber threats. By doing all these things and by looking at the landscape, we see that, at least for now, cyber is an additive thing.
The reality is that cyber tools have become more useful by big states against small states or individuals within their state — not between two peer adversaries.
But the reality is that we need to do much more work, and our views are likely to change as we find more evidence. As digital connectivity and the internet becomes more important to individuals in daily life, it becomes more of a vulnerability. That’s a challenge. In fact, the Chinese now view their main cybersecurity threat not as an oppositional threat from the United States, but as an internal threat, in terms of collective mobilization against their regime. The reality is that cyber tools have become more useful by big states against small states or big states against individuals within their state — not between two peer adversaries.
BRINK: In May, Wolfgang Kleinwächter, a former director on the ICANN board, wrote a piece for BRINK in which he outlined his concern that bad actors are moving from attacks confined to cyberspace to attacks on the internet’s infrastructure. He viewed attacking this infrastructure — which undergirds what is functionally a public utility — as a red line that shouldn’t be crossed. How does this threat figure into your analysis?
Dr. Valeriano: The red line, for me, is civilian death. And we need to have a conversation at some point as to what is too far, what exactly is illegal, and when do attacks start to harm civilians.
We have this norm in the international system that you don’t attack civilians. I hope that’s something that remains the same and that remains a norm. But given the critical failure points that the internet infrastructure is built upon, this can be a challenge. The internet is not a free domain where you can just fire at anyone at will. You’re likely to hit a civilian when you do these sorts of cyber fires.
I’d agree that there are some problems with attacking something that is so widely used by civilians and is so important to critical works. The problem is that that’s a very Western perspective, and that’s not necessarily something that the Russians and the Chinese believe. That’s a challenge because often when strategic analysis is done, it’s done with Western biases that may not fit into the reality of how other countries operate.
BRINK: You write that the international system is developing a norm against the use of cyber warfare. How do you see this norm manifesting itself?
Dr. Valeriano: I want to be very careful about the use of the term warfare. The majority of the time we use the term warfare, we mean to say political warfare, which is espionage and covert operations. And there’s no norm against that. Spying is one of the oldest professions in the world, and it’s not going away.
Now, there are a lot of norms that we have just come to accept. Stances against biological weapons or nuclear warfare have just become de facto norms because they make so much sense. You don’t want to launch nuclear weapons on the battlefield because it’s tough to contain the nuclear fallout. There are functional norms against devastating weapons.
I think the same thing is happening in cyberspace. There’s a functional norm against devastating attacks that would degrade critical facilities in the digital domain, precisely because they’re so devastating that they will likely engender retribution. I think that’s the critical moment we’re on now. A lot of people talk about “cyber Pearl Harbor,” or unleashing a “cyber Pandora’s box.” But the reality is that we haven’t seen anything like that.
BRINK: One of the distinctions you’ve drawn is between state and nonstate cyber actions. That line seems a bit blurry. There are businesses that are entangled or dependent on the work of the state. What should these enterprises be concerned with? Is it an internal lack of cyber hygiene? Should they be on alert about espionage or attacks?
Dr. Valeriano: One of the most basic mistakes I see is the assumption that your IT department is your cybersecurity department. Those things are not the same. There are things you need to do to protect your networks that companies are not doing — and these are the things they need to watch out for.
Now, a lot of nonstate actors who operate in major states like Russia, China and the United States are invariably co-opted by their national governments at some point. And states are responsible for the violence that comes out of them. That’s something we need to look out for in the future. Consider, for example, the idea that if a company gets hacked, that they’re going to hack back and find the root of the problem and nip it in the bud. We don’t want companies making foreign policy. We want foreign policy to be made by a clear national decision-maker who takes responsibility for these actions.
That’s something we need to keep in mind as we move forward, because things are going to get a lot more difficult in the future, and they’re going to get a lot more messy, and they’re going to get a lot more confusing. We’ve maintained a remarkable, stable system for the last 60, 70 years. We can only keep that up by being careful about the weapons we unleash on this world.
This interview has been edited and condensed for clarity.





