How to Mitigate Risks Associated with Trade Secret Theft
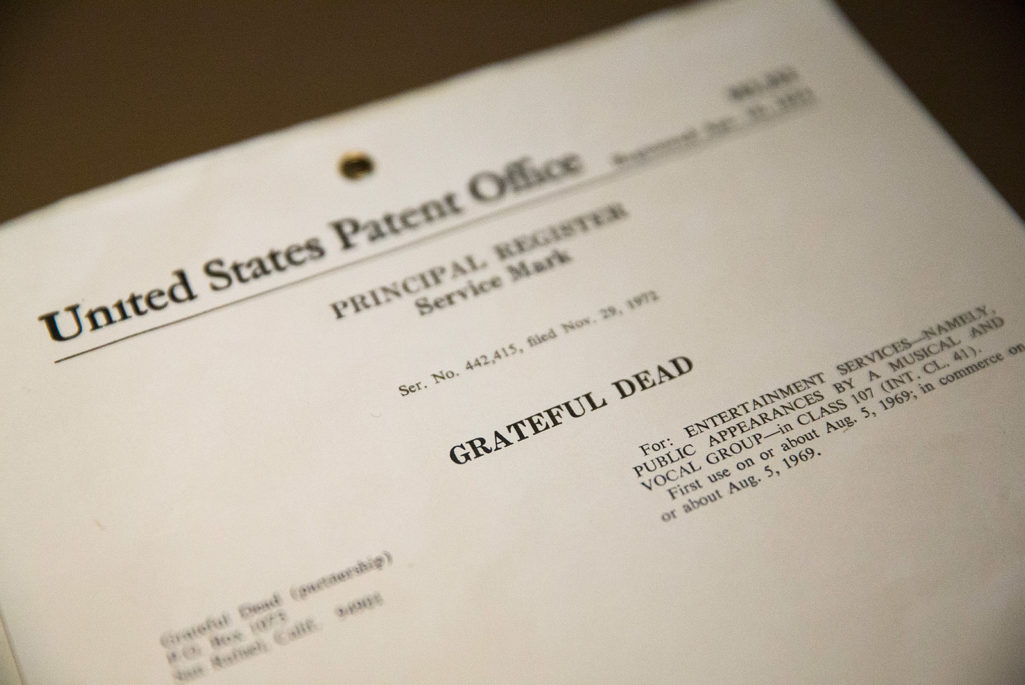
The original U.S. Patent & Copyright embossed document registering ownership of the name 'Grateful Dead' is prepared for auction on March 27, 2015. The document and other items will be offered for sale with a trove of other Grateful Dead memorabilia at a two-day sale on August 11 and 12.
Photo: Scott Olson/Getty Images
When companies think of securing their intellectual property today, most think about strengthening the barricades between their computer networks and the Internet to thwart cyberattacks, a task left largely to the IT team.
But internet security isn’t the same as intellectual property (IP) protection. Rarely does the IT team include IP protection and risk management among the objectives of their security systems—but they should.
The scope and quality of a company’s risk assessment and risk management efforts are important in identifying, prioritizing and implementing trade secret protections. Increasingly, risk management efforts are cited in court cases in a number of countries as part of the “reasonable steps” companies have taken to demonstrate adequate protection of company trade secrets.
Many companies, however, do not examine intellectual property risks in any detail, or they consider them only in isolation without reference to other types of security or compliance risks. Others fail to consider how to manage the IP-related risks in their supply chain or with other key third parties.
How to Incorporate Risk Management to Protect IP
Create an Inventory
As with other types of risk management, IP risk management begins with identifying the items at risk—the proprietary information a company deems to be its valuable trade secrets. Identification typically involves creating an inventory or registry of trade secrets.
Courts have looked at the question of whether companies have included particular material in an internal trade secrets registry as evidence of whether that material was confidential and whether “reasonable efforts” were taken to maintain that confidentiality.
Companies should take an inventory of relevant intellectual property, including both the IP that the company itself owns and the relevant third-party IP that the company manages or uses. Remember to identify each department or location within the company and each third party partner that deals with the most critical IP in the inventory.
Determining how likely each risk may occur is important in determining whether and how that risk should be addressed.
Assess Risks: What Happens if Company IP is Stolen?
After an inventory is created, a cross-section of company representatives should assess which trade secrets are most at risk of being taken, used or disclosed without authorization, why, and by whom. This may include internal personnel, supply chain companies or staff, or other external parties such as competitors, hacktivists or nation states.
Determining how likely each risk may occur is important in determining whether and how that risk should be addressed. The likelihood of IP theft can often be determined based on objective elements such as the controls currently in place, previous incidents, equipment or system tolerances or failure rates, industry data, benchmarking, or probability models.
Many of the risks inside a company or in a supply chain are linked to human behavior, which is not always predictable, so subjective experience and judgment comes into play.
The other major element of risk assessment is estimating how serious the damage or negative impact on the business would be if the risk were actually realized. Many companies use designations such as low, medium or high, or a scale of one to four or five, in categorizing the potential consequences of a risk.
Risk assessments are sometimes overly general (e.g. determining risk likelihood only on the basis of the particular country in which a supplier is located), done only as one off investigations when a supplier is appointed, or done without any specific consideration of IP-related risks.
Create and Implement a Risk Mitigation Plan
After risks are ranked, companies should develop and implement a risk mitigation plan to address a response to the most important risks the company faces. The purpose of the risk mitigation plan is to reduce risk by decreasing the likelihood of the negative event occurring and the impact that results if it does occur.
The plan should include deciding what risk response (if any) to take to address these risks and implementing those steps in the company’s management systems. Company leaders should notify employees of relevant information and set up an ongoing monitoring and review plan to ensure that those steps are carried out and updated.
Many companies typically decide whether to “avoid, minimize or offset” each risk, and determine which of the range of possible risk responses they will take for each risk. These can include:
- Discontinuing particular activities to avoid the risk
- Implementing various types of safeguards
- Sharing the risk with others to minimize risk (e.g. through outsourcing particular activities)
- Seeking ways to offset the negative impact
A company may decide to take no action. Even if this is the case, the risk assessment is critical to allowing the company to make a conscious decision to accept the risk and “do nothing.”
Risk response should involve concrete implementation plans that involve all management systems and controls relevant to the particular risks, which can range from different corporate policies and procedures through to financial, recordkeeping and information technology controls, to personnel and supply chain requirements. Typically the incident response plan covers what to do during the event, how to minimize the ongoing damage from the event, and how to change the management systems to reduce the severity and probability of it happening again.
Today, many companies are implementing specific standards and strategies for their corporate IT system to reduce the risk of trade secret theft. Some of these actions include installing new servers and firewalls; segregating or encrypting sensitive data; limiting access to particular personnel, and establishing emergency protocols if a trade secret is stolen.
Risk Assessment: a “Reasonable Step”
Beefing up your network security is one step to protect a company’s intellectual property from being stolen. As cyber and insider threats continue to climb, executives need to create a proactive risk assessment and mitigation plan that covers internal operations and extends to third parties. Such actions are likely to be viewed as “reasonable steps” taken to protect your trade secrets in the event of litigation. There are additional benefits as well: taking this approach is a smart and effective way to build capacity and resilience in your organization to protect against, and respond to, the growing and evolving threat of trade secret theft.




